Two big things usually cause people to call me at my computer service company and say they need help with their Wi-Fi: 1. Low signal density (bars) and 2. Low speeds (low Mbps).
Two big things usually cause people to call me at my computer service company and say they need help with their Wi-Fi: 1. Low signal density (bars) and 2. Low speeds (low Mbps).
Wi-Fi uses short-range radio waves to deliver internet access throughout your home. While it can feel almost “magical,” it’s still bound by physics. Signals weaken over distance, struggle to pass through certain materials, and are easily disrupted by interference. The result is slow speeds, dropped connections, buffering, and frustrating dead zones.
Understanding 2.4 GHz vs 5 GHz
2.4 GHz and 5 GHz Wi-Fi come down to a trade-off between range and speed. 2.4 GHz reaches farther and passes through walls better, but it’s slower and more prone to interference from devices like microwaves, Bluetooth, and nearby networks. 5 GHz, on the other hand, offers faster speeds and less interference, but it has a shorter range and weaker signal through walls.
In general, use 2.4 GHz for devices farther from the router or for basic connectivity, and 5 GHz for faster activities like streaming or gaming when you’re closer to the router.
What is a Dead Zone?
A dead zone is any area of your home where you should have Wi-Fi coverage but don’t, so you have “low signal density.”
What I do as a computer repair technician is walk through the home with a phone, tablet, or laptop and observe your signal strength and speed. You’ll quickly notice where performance drops off. If you have four bars, each bar represents a 25% signal measurement. If you have five bars, each is 20%, right? So you can calculate your drops as you walk through the house. If you are all the way out at your mailbox and you still have four of four bars, you have good signal density.
What Causes Low Signal Density or Poor Mbps Download Speeds?
- Your home is large: Bigger homes, multi-story layouts, and long floor plans are difficult to cover with a single router, especially if it’s located in one corner or tucked away. Often you need an upgraded router if you have over 3,500 square feet.
- Building materials block signals: Certain materials absorb or reflect Wi-Fi signals, including plaster walls such as those in older homes or those with wire mesh, brick, concrete, stone, metal, and even large mirrors or aquariums.
- Electronic interference is everywhere: Common sources of interference include microwaves, baby monitors, wireless security systems, Bluetooth devices, and older cordless phones. In today’s homes, the number of connected devices has increased dramatically, adding more congestion.
- Network congestion in your area: If you live in a neighborhood with many nearby networks, overlapping Wi-Fi signals can slow your connection due to channel interference.
- Your router is outdated or failing: Older routers often can’t keep up with modern demands like streaming, gaming, video calls, and smart home devices. Hardware can also degrade over time and cause inconsistent performance.
- Your internet provider may be the issue: Sometimes the problem isn’t inside your home. Issues with your modem, wiring, or ISP can result in slow or unstable service. So sometimes it can be a problem outside of the house.
- You might not be paying for much of a plan: Make sure you’re paying for at least 200 Mbps service from your ISP. Most areas have 1,000 Mbps plans now or even higher. You can test your internet speed here for free.
How To Fix Wi-Fi Dead Zones
- Reposition your router: Place your router in a central location. Higher is better, so elevate it off the floor, and avoid basements or corners. Proper placement alone can significantly improve coverage.
- Upgrade to a modern router or mesh system: Mesh Wi-Fi systems are now one of the best solutions for larger homes. They use multiple units to create consistent coverage throughout the house. Upgrading to Wi-Fi 6 or newer can make a noticeable difference.
- Reduce interference and optimize placement: Keep your router away from large metal objects and other electronics. Use less congested channels and take advantage of 5 GHz or 6 GHz bands when available.
- Use Ethernet where possible: Wired connections provide the fastest and most stable performance. This is especially useful for desktops, TVs, and gaming systems.
- Test your internet speed and equipment: Run a speed test directly from your modem and compare it to your Wi-Fi speeds. Restart your equipment and make sure your modem supports your current internet plan.
- Upgrade your plan: Make sure you’re paying for at least 200 Mbps service from your ISP. Most areas have 1,000 Mbps plans now or even higher.
Wi-Fi dead zones are extremely common, especially in larger or older homes, but they can almost always be fixed. Sometimes the solution is simple, like moving your router, and other times it may require upgraded equipment or a better network layout. Either way, improving your Wi-Fi setup can make your entire home faster, more reliable, and far less frustrating to use.

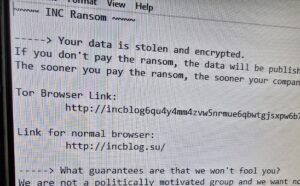 I just did a job at a lawyer’s office in Louisville where all the data on the server was encrypted. They almost lost everything. It was a password compromise issue. As more of our lives move online, internet security has become one of the most critical concerns for both individuals and businesses. Cybercriminals are constantly evolving their methods, often relying on simple but highly effective techniques to gain unauthorized access to accounts and systems.Understanding how these attacks work is the first step toward protecting yourself or your organization.
I just did a job at a lawyer’s office in Louisville where all the data on the server was encrypted. They almost lost everything. It was a password compromise issue. As more of our lives move online, internet security has become one of the most critical concerns for both individuals and businesses. Cybercriminals are constantly evolving their methods, often relying on simple but highly effective techniques to gain unauthorized access to accounts and systems.Understanding how these attacks work is the first step toward protecting yourself or your organization.