In the rapidly evolving landscape of technology, computer repair businesses play a crucial role in ensuring the smooth functioning of devices and safeguarding valuable data. Louisville Laywer John Olash says: “While the focus is often on technical expertise, it’s equally important for computer repair shops to navigate the intricate web of legal responsibilities.” This guide aims to shed light on the key legal obligations and responsibilities that computer repair businesses should be aware of to operate ethically and within the bounds of the law.
In the rapidly evolving landscape of technology, computer repair businesses play a crucial role in ensuring the smooth functioning of devices and safeguarding valuable data. Louisville Laywer John Olash says: “While the focus is often on technical expertise, it’s equally important for computer repair shops to navigate the intricate web of legal responsibilities.” This guide aims to shed light on the key legal obligations and responsibilities that computer repair businesses should be aware of to operate ethically and within the bounds of the law.
1. Data Protection Laws
Overview:
Data protection is a paramount concern in the digital age. Repair shops often handle sensitive customer data, making it imperative to comply with data protection laws. Familiarize yourself with local and national regulations, such as the General Data Protection Regulation (GDPR) or the Health Insurance Portability and Accountability Act (HIPAA), depending on your jurisdiction and the nature of the data you handle.
Practical Tips:
Obtain explicit consent from customers before accessing or storing any personal or sensitive information.
Implement robust data security measures to prevent unauthorized access or data breaches.
Regularly update privacy policies to reflect any changes in data handling practices.
2. Customer Privacy
Overview:
Respecting customer privacy is not just good business practice; it’s a legal requirement. Repair technicians must strike a balance between providing effective services and preserving the confidentiality of customer information.
Practical Tips:
Louisville attorney John Byrnes says “Clearly communicate your privacy policy to customers and ensure they understand how their data will be handled.
And restrict access to customer information only to authorized personnel.”
Train staff on the importance of customer confidentiality and data protection.
3. Consumer Rights
Overview:
Understanding and respecting consumer rights is essential for building trust and avoiding legal complications. Consumers have rights regarding the quality of service, timely repairs, and transparent pricing.
Practical Tips:
Provide clear and detailed estimates before commencing repairs, including potential additional costs.
Clearly outline warranty terms and conditions to manage customer expectations.
Respond promptly to customer inquiries and complaints, addressing any concerns with transparency.
4. Documenting Repairs and Transactions
Overview:
Maintaining accurate records of repairs and transactions not only ensures transparency but also serves as a legal safeguard in case of disputes.
Practical Tips:
Develop a standardized system for documenting repairs, including the issues identified, services provided, and any replaced components.
Issue detailed invoices that include a breakdown of charges, ensuring clarity for both parties.
Retain records for a legally required period, as per local regulations.
Conclusion
In the world of computer repair, technical proficiency must go hand-in-hand with legal compliance. By proactively addressing data protection, customer privacy, consumer rights, and documentation practices, computer repair businesses can build a solid foundation for ethical operations. Staying informed about the legal landscape and regularly updating policies will not only protect the business but also foster trust with customers. As technology continues to advance, navigating legal responsibilities will remain a cornerstone of successful computer repair businesses.
Author Archives: Chris Calkins
Demystifying Tech Jaron: A Glossary of Common Computer Terms
 Technology has become an integral part of our daily lives, but its complex vocabulary can sometimes be overwhelming and confusing. We often encounter unfamiliar terms and acronyms that leave us scratching our heads. To help demystify the jargon, here’s a glossary of common computer terms that everyone should know.
Technology has become an integral part of our daily lives, but its complex vocabulary can sometimes be overwhelming and confusing. We often encounter unfamiliar terms and acronyms that leave us scratching our heads. To help demystify the jargon, here’s a glossary of common computer terms that everyone should know.
1. Operating System (OS): Software that manages computer hardware and software resources and provides common services for computer programs. Examples include Windows, macOS, and Linux.
2. Browser: A software application used to access and view websites on the internet. Popular browsers include Google Chrome, Mozilla Firefox, and Apple Safari.
3. Firewall: A network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted internal network and an untrusted external network, such as the internet.
4. Cloud Computing: The delivery of computing services—including servers, storage, databases, networking, software, and analytics—over the internet (“the cloud”) to offer faster, more flexible, and scalable resources.
5. Cookies: Small pieces of data sent from a website and stored on a user’s computer by the user’s web browser while the user is browsing. Cookies are used to remember state information or to record the user’s browsing activity.
6. Virus: A type of malicious software program that, when executed, replicates by modifying other computer programs and inserting its own code. Viruses can cause harm to a computer system, such as corrupting data or stealing personal information.
7. Router: A networking device that forwards data packets between computer networks. Routers perform the traffic directing functions on the internet by sending data to its intended destination based on the IP address and other routing information.
8. RAM (Random Access Memory): A form of computer memory that can be read and changed in any order, typically used to store data temporarily while a computer is running. In simple terms, RAM is what allows a computer to multitask and run programs efficiently.
9. URL (Uniform Resource Locator): The address used to access resources on the internet, such as a website or a file. A URL indicates the protocol used to access the resource, the location of the server, and the specific file or resource being accessed.
10. Encryption: The process of converting information into a code to prevent unauthorized access. Encryption protects sensitive data by rendering it unreadable to anyone without the necessary decryption key.
11. Bluetooth: A wireless technology standard for exchanging data over short distances from fixed and mobile devices, creating personal area networks (PANs). It is commonly used for connecting devices such as smartphones, headphones, and speakers.
12. Cache: A hardware or software component that stores data so that future requests for that data can be served faster. Caching can significantly improve the performance and responsiveness of a system.
13. Ethernet: A system for connecting a number of computer systems to form a local area network (LAN), with protocols to control the passing of information and to avoid simultaneous transmission by two or more systems.
14. HTML (Hypertext Markup Language): The standard markup language for documents designed to be displayed in a web browser. It can be assisted by technologies such as Cascading Style Sheets (CSS) and scripting languages such as JavaScript.
15. VPN (Virtual Private Network): A secure and private connection that enables users to send and receive data across shared or public networks as if their computing devices were directly connected to a private network. VPNs are commonly used to protect online privacy and secure internet connections, especially when using public Wi-Fi networks.
Understanding these common computer terms can empower individuals to navigate and comprehend the world of technology more confidently. As technology continues to evolve, having a foundational understanding of these terms will help bridge the gap between the tech-savvy and those less familiar with the fast-paced and ever-changing landscape of digital innovation.
When Buying A New PC Do Not Focus On Intel i3, i5, or i7 Designation
 When it comes to choosing a new computer or laptop, the processor is often one of the most important factors to consider. Intel’s processors, particularly the i3, i5, and i7 series, are some of the most popular and widely used in the industry. However, many people overlook the significance of the numbers that come after these designations, which actually represent the generation of the processor. Focusing on the generation of the processor is crucial for several reasons.
When it comes to choosing a new computer or laptop, the processor is often one of the most important factors to consider. Intel’s processors, particularly the i3, i5, and i7 series, are some of the most popular and widely used in the industry. However, many people overlook the significance of the numbers that come after these designations, which actually represent the generation of the processor. Focusing on the generation of the processor is crucial for several reasons.
First and foremost, the generation of the processor tells you the age. I’ve noticed recently especially on Amazon people are trying to pass off computers as new that are acutally “renewed” or used or have NOS (new old stock) parts in them. Hey, there is nothing wrong with a 8th Gen i7, or 9th Gen, it’s just important to know that it is not the same as a 12th gen. If you’re buying it on Amazon or Ebay and it’s a 8th gen something is up.
In addition, the generation of the processor can also affect its compatibility with other hardware and software. Newer generations of processors often come with updated architectures and instruction sets, which can lead to better compatibility with the latest hardware components and software applications. This is particularly important for tasks such as gaming, video editing, and 3D rendering, where compatibility and performance capabilities are critical.
Furthermore, focusing on the generation of the processor is essential for future-proofing your investment. By choosing a newer generation processor, you can ensure that your computer or laptop will remain relevant and capable for a longer period of time. This is particularly important for those who rely on their devices for demanding tasks or for professional use, as the performance gap between newer and older generation processors continues to widen over time.
It’s also worth noting that newer generations of processors often come with enhanced security features, which can be crucial for protecting sensitive data and maintaining the integrity of your system. As cyber threats continue to evolve and become more sophisticated, having a processor with the latest security capabilities is essential for safeguarding your digital assets and privacy.
In conclusion, the numbers that come after Intel’s i3, i5, and i7 designations represent the generation of the processor, and focusing on these numbers is crucial for ensuring optimal performance, compatibility, and future-proofing. Whether you are in the market for a new computer or looking to upgrade your existing one, considering the generation of the processor is an important factor in making an informed and effective decision. By staying informed about the latest advancements in processor technology, you can ensure that you are getting the best possible performance and features from your device.
If you need help buying a new PC in Louisville Kentucky or surrounding areas feel free to give me a call at (502)963-3981
How to Uninstall McAfee Antivirus on Windows 11
 McAfee antivirus software may need to be removed for various reasons. Not the least of which it causes dysfunction in your software environment, acts like a virus itself and slows your computer down to a crawl.
McAfee antivirus software may need to be removed for various reasons. Not the least of which it causes dysfunction in your software environment, acts like a virus itself and slows your computer down to a crawl.
Here’s a step-by-step guide on how to uninstall McAfee from your Windows 11 system:
Step 1: Access Settings
Click on the Start Menu located at the bottom left corner of your screen.
Select the gear-shaped Settings icon to open the Settings menu.
Step 2: Open Apps
In the Settings menu, select Apps from the list on the left-hand side.
Step 3: Locate McAfee Software
Scroll down the list under “Apps & features” to find the McAfee antivirus software.
Click on the McAfee application to reveal the options.
Step 4: Uninstall McAfee
After selecting McAfee, a submenu will appear. Click on the Uninstall button.
Step 5: Confirmation Prompt
A confirmation prompt will appear asking if you want to allow this app to make changes to your device. Click Yes to proceed with the uninstallation.
Step 6: McAfee Uninstallation Process
The McAfee uninstaller will open. Follow the on-screen instructions to complete the uninstallation process. This may involve confirming your choice and waiting for the software to be removed from your system.
Step 7: Reboot Your System (if prompted)
After the uninstallation is complete, you may be prompted to restart your computer. If so, click on the Restart Now button to reboot your system.
Step 8: Verify McAfee is Uninstalled
Once your system restarts, check the Apps list in Settings again to ensure McAfee is no longer listed among your installed applications.
Congratulations! You’ve successfully uninstalled this garbage from your Windows 11 computer.
Does the Dell XPS 8940 Support Gen 5 M.2 Drives?
Recently, I got this question from a client. No, the Dell XPS 8950 desktop computer does not support Gen 5 M.2 PCIe SSDs. The motherboard in the XPS 8950 is the Dell Z960, which only supports up to Gen 4 PCIe. This means that while you can use a Gen 4 M.2 PCIe SSD in your XPS 8950, you will not be able to take advantage of the faster speeds that Gen 5 SSDs offer.Here are some resources that confirm this:
Dell XPS 8950 Manual: The manual for the XPS 8950 states that the M.2 slots support PCIe Gen 3 x4 and PCIe Gen 4 x4 SSDs, but makes no mention of Gen 5 support.
Dell XPS 8950 Specifications: The specifications page for the XPS 8950 on the Dell website also lists the M.2 slots as supporting PCIe Gen 3 x4 and PCIe Gen 4 x4 SSDs.
Dell Community Forum: There is a thread on the Dell Community Forum where users have discussed the fact that the XPS 8950 does not support Gen 5 M.2 PCIe SSDs.
If you are looking for a desktop computer that supports Gen 5 M.2 PCIe SSDs, you will need to choose a different model. Some newer Dell XPS models, such as the XPS 8960, do support Gen 5 M.2 PCIe SSDs.
What is Bitlocker and How to Turn It Off?
 BitLocker is a security feature in Windows that allows you to encrypt your hard drive to protect your data from unauthorized access. When you enable BitLocker, you are required to generate a recovery key to unlock your encrypted drive in case you forget the password or encounter a system failure. The problem is you usually only encrypt the data against yourself. TURN IT OFF. Unless you’re in the FBI or a top secret industry and usually even then it’s only going to cause you a problem later on.
BitLocker is a security feature in Windows that allows you to encrypt your hard drive to protect your data from unauthorized access. When you enable BitLocker, you are required to generate a recovery key to unlock your encrypted drive in case you forget the password or encounter a system failure. The problem is you usually only encrypt the data against yourself. TURN IT OFF. Unless you’re in the FBI or a top secret industry and usually even then it’s only going to cause you a problem later on.
Here’s a guide on how to turn off BitLocker encryption:
1. Open the Control Panel: Click on the Start button and select Control Panel from the menu. Alternatively, you can search for Control Panel in the Windows search bar.
2. Click on “System and Security”: In the Control Panel, click on “System and Security” to access the BitLocker Drive Encryption settings.
3. Turn off BitLocker: Under the BitLocker Drive Encryption section, you’ll see an option to “Turn off BitLocker.” Click on this option to begin the process of turning off the encryption.
4. Enter the recovery key: If prompted, you will need to enter the recovery key that you created when you initially set up BitLocker. This key is crucial for unlocking the encrypted drive when BitLocker is turned off.
5. Turn off BitLocker for the drive: After providing the recovery key, you will be given the option to turn off BitLocker for the selected drive. Select the drive that you want to disable BitLocker for and click “Turn off BitLocker.”
6. Confirm turning off BitLocker: You will then be prompted to confirm the action of turning off BitLocker encryption. Click “Decrypt the drive” to confirm and initiate the process of decrypting the drive.
7. Wait for decryption: Depending on the size and speed of your drive, the decryption process may take some time. It’s important not to interrupt this process, as doing so could result in data loss or corruption.
Once the decryption process is complete, your drive will no longer be encrypted with BitLocker. You will no longer need to enter your recovery key to access your files, and the encryption key will be turned off.
A Journey Through Time: Unveiling the History and Purpose of Web Browsers
 In today’s digital age, web browsers have become an essential tool through which we access information, communicate with others, and navigate the vast landscape of the internet. While influential browsers such as Edge, Internet Explorer, Google Chrome, Safari, and Firefox dominate the market, the historical evolution and underlying purposes of these browsers have significantly shaped our online experiences. This article aims to take you on a captivating journey through time, exploring the origins, milestones, and distinct features of these popular web browsers.
In today’s digital age, web browsers have become an essential tool through which we access information, communicate with others, and navigate the vast landscape of the internet. While influential browsers such as Edge, Internet Explorer, Google Chrome, Safari, and Firefox dominate the market, the historical evolution and underlying purposes of these browsers have significantly shaped our online experiences. This article aims to take you on a captivating journey through time, exploring the origins, milestones, and distinct features of these popular web browsers.
I. The Early Days: From Mosaic to Internet Explorer
The web browsing journey began with Mosaic, a pioneering browser developed in the early 1990s by the National Center for Supercomputing Applications (NCSA). However, it was Internet Explorer (IE), released in 1995 by Microsoft, that played a pivotal role in familiarizing the masses with web surfing. As the default browser on Windows, IE quickly achieved widespread adoption while embodying the basic web browsing principles of that era.
II. The Rise of Firefox and Safari
In 2004, Mozilla Firefox emerged as a strong contender in the browser market, offering enhanced security, privacy, and customization options. Built upon open-source principles, Firefox challenged the dominance of IE and introduced a more user-centric experience. Around the same time, Apple introduced Safari, exclusively for Mac systems. Safari swiftly gained popularity due to its efficient performance, sleek design, and seamless synchronization with other Apple devices.
III. Chrome’s Revolution: Speed, Simplicity, and Stability
In 2008, Google Chrome entered the arena, revolutionizing web browsing with its minimalist design, speed, and stability. By introducing a multiprocess architecture, Chrome improved performance and security, allowing users to enjoy a seamless browsing experience. Chrome quickly became the browser of choice for many, dominating the market with its continuous updates and offering extensive customization through a range of extensions.
IV. Edge: Microsoft’s Modern Reinvention
As the successor to Internet Explorer, Microsoft Edge made its debut in 2015, aiming to bring a fresh and modern browsing experience to Windows users. Determined to provide speed, security, and compatibility, Edge was designed to be a lightweight, user-friendly browser. Embracing the Chromium open-source project in 2018 brought significant improvements, enabling Edge to compete with other popular browsers, offering a customizable interface and an extensive library of extensions.
V. The Broader Impact: Advancing Web Standards and User Experience
While each browser has its unique features and design, collectively, these web browsers have worked towards advancing web standards, improved security, and a seamless user experience. Through various iterations, they have pushed the boundaries of web browsing, enabling compatibility with emerging technologies, such as HTML5, CSS, JavaScript, and more.
Conclusion:
Web browsers have come a long way since their inception, continually adapting to meet the evolving needs of users and the challenges posed by an ever-changing internet landscape. From Internet Explorer’s pioneering dominance to the sophistication of Edge, Chrome, Firefox, and Safari, each browser has played a crucial role in making the web accessible to billions of people worldwide. As technology and user requirements continue to evolve, the future of web browsing promises further innovation and optimization, ensuring an even richer online experience for all.
Cracking the Code: Unraveling 10 Uncommon Factors Affecting Your Home Network
 Introduction: In the era of advanced technology and increasing reliance on home networks for various tasks, encountering network issues can be frustrating. While most common network problems can be easily resolved, there are a few lesser-known culprits that may be affecting your home network performance. Take a deep dive with us as we explore ten unique factors that might be playing a role in your network troubles.
Introduction: In the era of advanced technology and increasing reliance on home networks for various tasks, encountering network issues can be frustrating. While most common network problems can be easily resolved, there are a few lesser-known culprits that may be affecting your home network performance. Take a deep dive with us as we explore ten unique factors that might be playing a role in your network troubles.
1. Aged Firmware: Outdated firmware in your router can cause compatibility issues and hinder network performance. Ensure you regularly update your router’s firmware to stay ahead of potential problems.
2. DNS Hiccups: Domain Name Server (DNS) servers play a vital role in translating websites’ domain names to IP addresses. Opting for unreliable or overloaded DNS servers might result in sluggish network speeds. Switching to reliable and fast DNS servers like Google DNS or Cloudflare DNS can help mitigate this issue.
3. Overburdened Network: An overcrowded network can impede your home network’s performance. Multiple devices simultaneously accessing the network can lead to congestion, slower speeds, and intermittent connectivity. Consider implementing Quality of Service (QoS) settings to prioritize critical devices or upgrade your internet package.
4. Sneaky Signal Interference: Unbeknownst to many, various household objects can interfere with Wi-Fi signals. Mirrors, metal objects, thick walls, and even larger appliances can disrupt signal strength. Assess your network placement and consider relocating your router to minimize interference.
5. Struggling Network Adapter: Outdated or malfunctioning network adapters can lead to poor network connectivity and speed. Ensure your devices are equipped with up-to-date and compatible network adapters to prevent this bottleneck.
6. Invasive Malware: Malware isn’t limited to affecting computers; it can also target routers. Malicious code injected into routers can compromise network security, degrade performance, and even redirect your internet traffic. Regularly update your router’s firmware, change default login credentials, and install reputable security software to ward off potential malware threats.
7. Unoptimized Wi-Fi Channels: Interference from neighboring wireless networks can slow down your Wi-Fi speeds. Using tools like Wi-Fi analyzers, identify the least congested channels and switch your Wi-Fi router to an optimized channel for improved performance.
8. Weather Woes: Extreme weather conditions such as heavy rain, intense lightning storms, or severe winds can physically damage or disrupt network equipment, leading to intermittent or complete network outages. Safeguard your networking equipment by ensuring proper insulation and protection from the elements.
9. Cryptic Cable Faults: Damaged or frayed network cables can cause connectivity issues. Ensure all cables are securely connected, properly insulated, and free from physical damage to maintain a reliable network connection.
10. Resource-Hungry Background Apps: Often overlooked, resource-intensive background applications on your devices can consume a significant portion of your network’s bandwidth, leading to slower internet speeds for other devices. Monitor and manage these apps, limiting their impact on your network performance.
Conclusion: Network issues can stem from various unexpected factors. By understanding the less common culprits affecting your home network, you can troubleshoot more effectively and address these issues proactively. Remain vigilant, keep your devices updated, and make informed decisions to ensure a stable and optimized home network experience.
Shielding Your System: Three Effective Ways to Ward off Computer Viruses
 Computer viruses present a persistent threat to our digital lives, capable of wreaking havoc on our devices and compromising our valuable data. To safeguard your system, it’s crucial to adopt effective preventive practices. In this article, we highlight three practical ways to avoid computer viruses, ensuring a safe and secure computing experience.
Computer viruses present a persistent threat to our digital lives, capable of wreaking havoc on our devices and compromising our valuable data. To safeguard your system, it’s crucial to adopt effective preventive practices. In this article, we highlight three practical ways to avoid computer viruses, ensuring a safe and secure computing experience.
1. Exercise Internet Savviness: Safe browsing practices play a pivotal role in fending off viruses. When accessing the Internet, exercise caution and adhere to the following guidelines: a) Be Vigilant With Downloads: Be cautious when downloading files or software, particularly from unfamiliar websites or unsolicited email attachments. Verify the legitimacy of the sources and place trust solely in reputable platforms. Avoid clicking on tempting pop-up ads or suspicious links that may direct you to potentially infected websites. b) Be Wary of Phishing Attempts: Cybercriminals often exploit phishing techniques to trick users into unknowingly downloading viruses or sharing sensitive information. Always scrutinize emails or messages asking for personal details or financial information. Legitimate organizations rarely request such information through unsolicited emails. Be skeptical of suspicious email addresses, grammatical mistakes, or unexpected urgency in the message.
2. Update Software Regularly: Ensure your Windows Operating System, web browsers, and other software are up to date with the latest security patches and bug fixes. These updates often contain critical security enhancements that protect against newly discovered vulnerabilities, reducing the risk of infection. Although these updates are often supposed to update automatically often times they do not. Learn how to manually check for Windows up
3. Practice Smart Data Backup Regimes: Data Backups provide an additional layer of protection against computer viruses. While they don’t prevent infection a data backup makes it easy to recovery from an infection that requires a complete OS Installation on your computer. Follow these best practices to reduce vulnerability: a) Regular Data Backup: Create backups of your essential files and folders periodically. Use external hard drives or flash drives for these backups. In the event of a virus attack or system compromise, having a recent backup ensures data recovery and minimizes potential loss..
Conclusion: By following these three practical ideas exercising internet savviness, updating software and practicing smart data backups- you can significantly reduce the risk of falling victim to computer viruses catastrophes. Remain proactive and vigilant in your cybersecurity efforts to safeguard your system and ensure a secure computing experience.
Transforming Windows 11: Five Methods to Recreate the Windows 10 Look
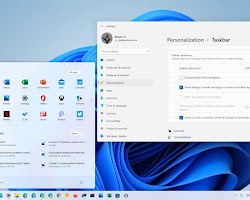
With the arrival of Windows 11, Microsoft has introduced a fresh and modernized operating system. While many users appreciate the updated design and features, some may prefer the familiar look and feel of Windows 10. Fortunately, there are ways to customize Windows 11 to resemble its predecessor. In this article, we will explore five methods to make Windows 11 look like Windows 10, complete with illustrative photos.
1. Restore the Start Menu:
The redesigned Start Menu in Windows 11 offers a centered layout, but if you prefer the classic left-aligned Start Menu from Windows 10, you can bring it back. To achieve this, you can install a third-party Start Menu customization tool, such as “Open Shell,” which emulates the Windows 10 Start Menu. By downloading and installing this utility, you can enjoy the familiar left-aligned Start Menu, similar to Windows 10.
2. Enable Taskbar Icons Alignment:
Windows 11 introduces a centered taskbar layout, a departure from the left-aligned taskbar in Windows 10. However, if you prefer the classic left-aligned taskbar, you can modify it. To accomplish this, right-click on an empty area of the taskbar, go to “Taskbar settings,” and under “Taskbar behaviors,” choose “Left” from the “Taskbar alignment” drop-down menu. This adjustment will realign the taskbar icons to the left, similar to Windows 10.
3. Customize the Windows Theme:
To further enhance the Windows 10 aesthetic in Windows 11, you can adjust the system theme. Open the “Settings” app and navigate to “Personalization.” Under the “Themes” section, choose “Windows 10” from the “Choose a theme” option. This selection will modify the visual elements, window borders, and colors to resemble the Windows 10 theme, giving your system a nostalgic touch.
4. Bring Back Live Tiles:
Windows 11 introduces a simplified, icon-based Start Menu, replacing the live tiles from Windows 10. If you miss the live tiles’ dynamic information and interactive functionality, you can reinstate them with the help of third-party tools. Tools like “Win10Tile” allow you to create and customize live tiles, enabling you to incorporate the beloved live tile experience into your Windows 11 environment.
5. Revert to the Classic File Explorer:
Windows 11 introduces a modernized File Explorer with a streamlined and simplified design. If you prefer the classic File Explorer appearance from Windows 10, you can restore it with ease. Right-click the File Explorer icon on the taskbar, then right-click “File Explorer” in the context menu and select “Properties.” In the Properties window, under the “Shortcut” tab, choose “Open file location.” This will open the File Explorer folder. Locate and double-click on the “explorer.exe” file, which will launch the classic File Explorer reminiscent of Windows 10.
Conclusion:
While Windows 11 brings a fresh look and exciting features, it’s understandable that some users may long for the familiarity of Windows 10. By implementing these five methods, you can transform Windows 11 into an environment that closely resembles its predecessor.